Device Intelligence Asset Inventory
Device Intelligence Asset Inventory
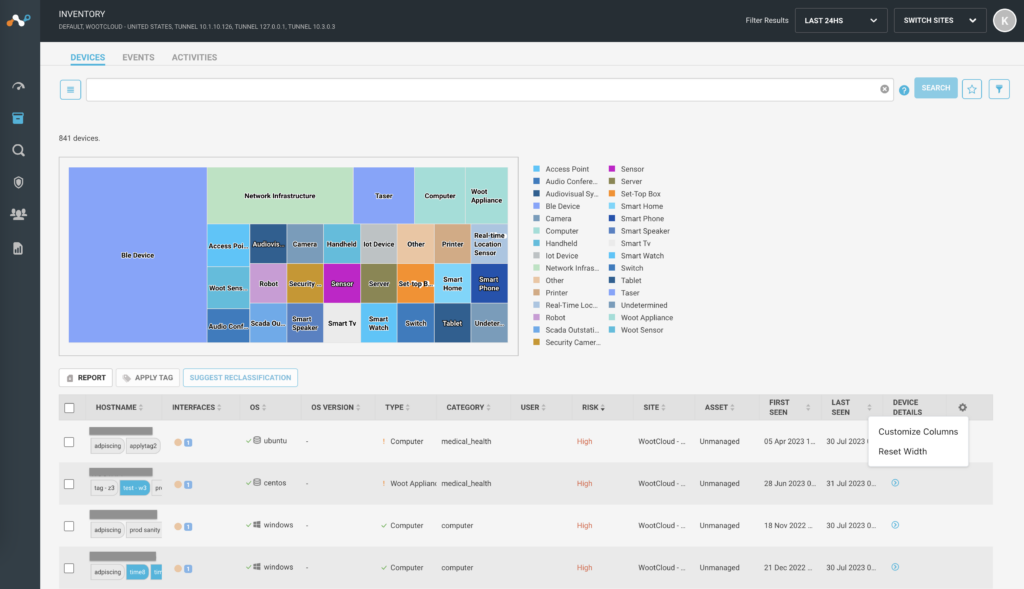
Navigate to the Inventory tab to see the assets captured in Device Intelligence. You can see the assets segregated in three different tabs:
-
Device View – display devices in Device Intelligence environment with the intellectual information like address, type, tags, users, etc.
-
Events View – display devices and events of those devices with vulnerabilities, packet alerts, anomalies, etc.
-
Activities View – display OT activities seen in the network like cold restart, write variable, etc. Refer OT Device Discovery article to learn more about it.
Discover Operational Technology (OT) in Device Intelligence is a controlled General Availability feature. Contact your Netskope sales representative/support to enable this feature for your tenant.
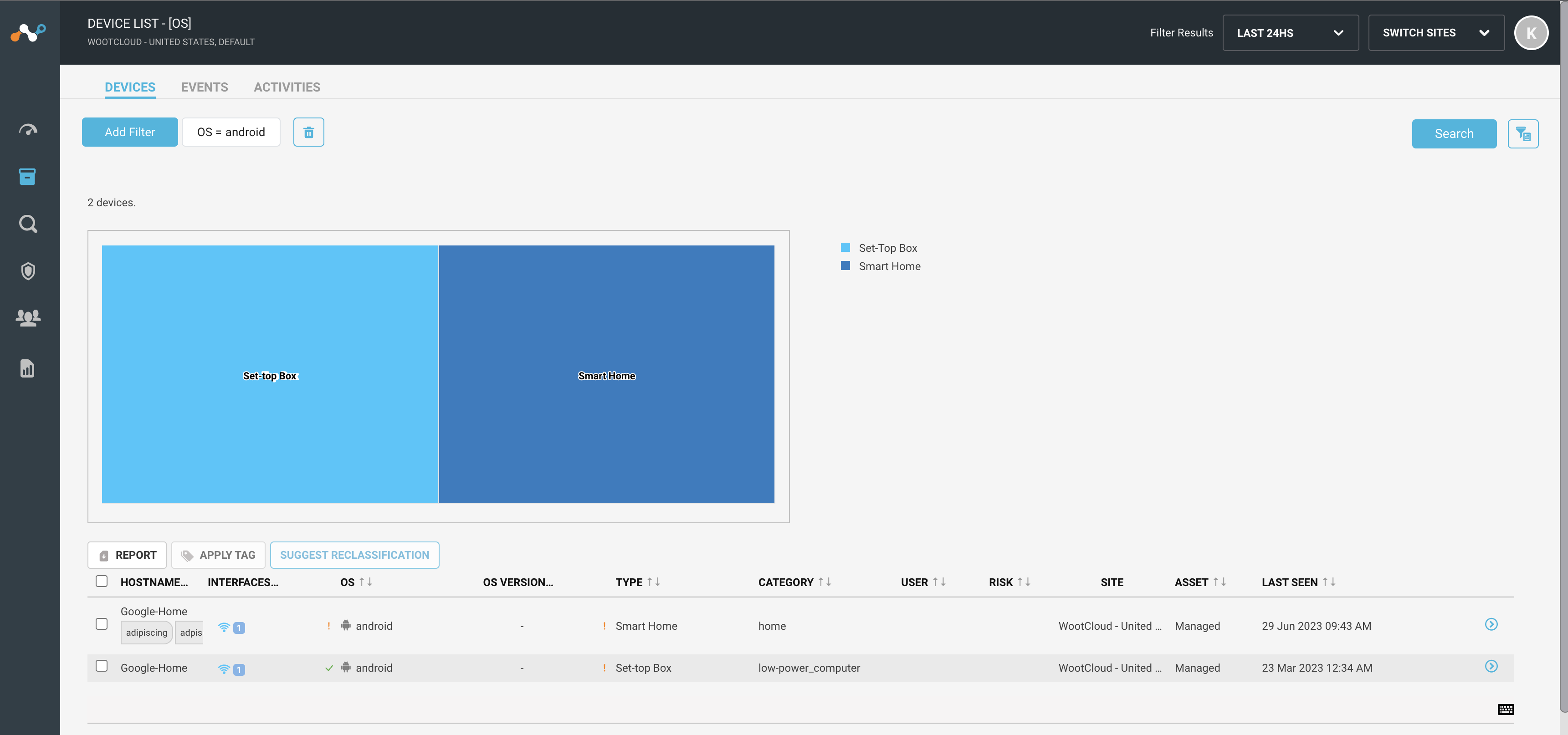
Device View
- You can see a chart with distinct devices in your environment and hovering on it will show the number of devices of that type.
- The following table shows the device details like host name, interface connection, operating system, type, risk of device, etc.
- You can click on the device to see the detailed device summary.
- Click on the Report button above the table to generate a report of the devices in excel or CSV format.
- You can select one or more devices in the table to apply or disable device tags using the Apply Tag button above the table. You can only apply the existing tags. To create new tags, navigate to the Manage > Tags menu.
- Click on the Suggest Reclassification button to generate a reclassification request.
- Adjust width of the table columns.
- Reset the width of the table columns to default by clicking Settings icon > Reset Width option.
- Customize the columns in the table. You can chose to display and hide the columns in the table by navigating to Settings icon > Customize Columns option.

Device Details
Click on the zoom-in icon beside the asset hostname > Details link from the device summary screen. You will see detailed information about the device on a new screen.


-
Hostname of the device
-
Type of the device
-
Management of the device, i.e. managed or unmanaged
-
Tags assigned to the device
-
Operating system of the device
-
Control of the device
-
Site of the device
-
Pie chart of the device with different issues and the risk score.
-
Device behavior – the chart quantifies the behavior of the device using seven features and compares it to the baseline values. These baseline values are calculated for each device-type by looking at all devices of that type across IoT Security. The visualization will help customers benchmark the device’s behavior w.r.t. the generic behavior of the corresponding device type. Additionally, deviations are indicated with a red marker at the end of the corresponding arm of the spider chart. For the current release the features are as given below. These are computed by averaging observed values for a window of one minute.
-
Average number of connections from the device
-
Count of the average number of packets sent to the server
-
Count of the average number of packets sent to the client
-
Total number of bytes sent
-
Total number of bytes received
-
Number of unique destination IP addresses connected to the device
-
Number of unique destination ports connected to the device
-
-
Device Context – list of parameters with device intellectual information.

-
Compliance of the device – it lists all service compliances configured in compliance settings page. The table shows the status as compliant, stale and non-complaint for every device.
-
Device interface information. If a device is connected by more than one interface, you will see the information in different tabs.
-
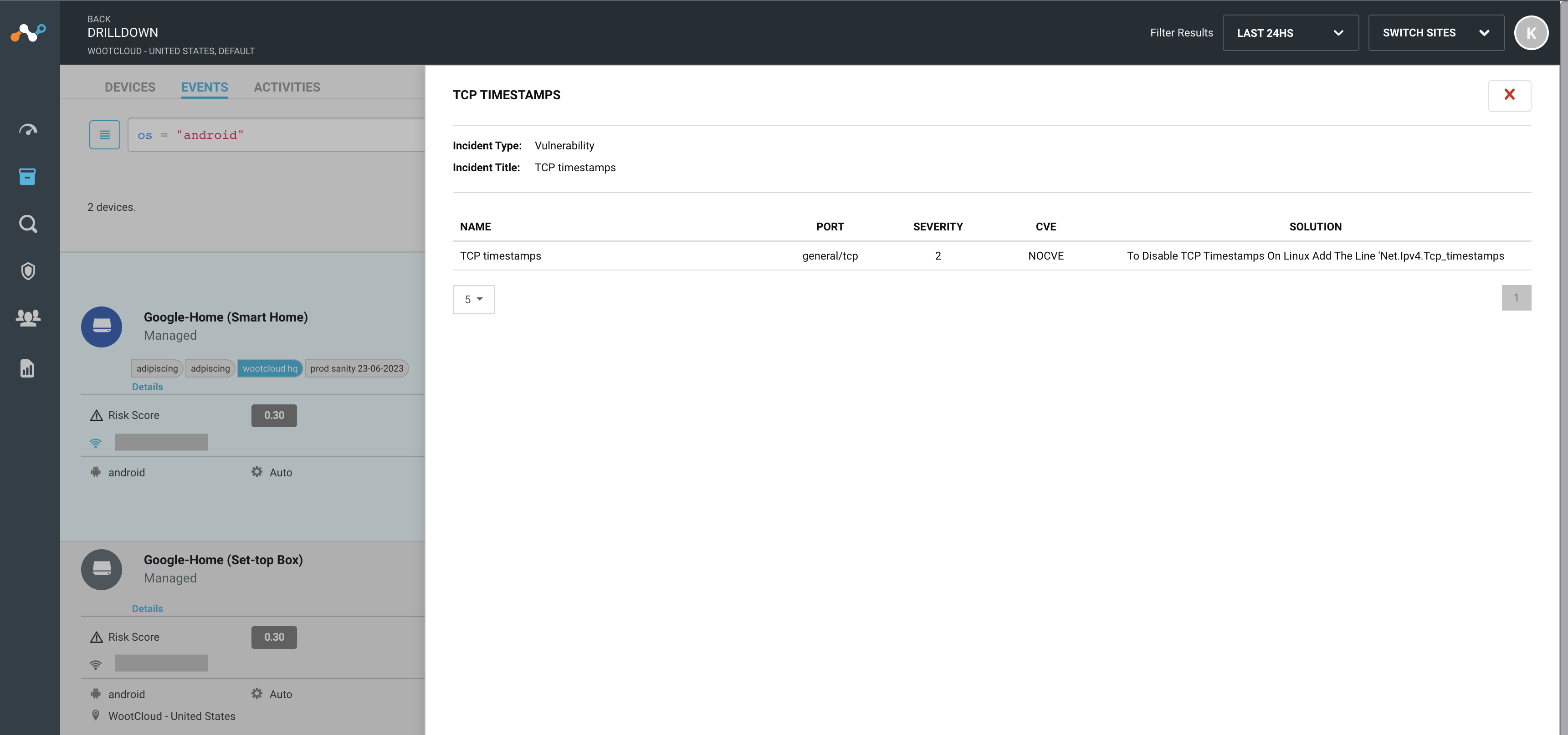
Risk Assessment of issues captured by the device, with the severity, incident type and number of occurrences of this issue.

-
Topology of Operational Technology devices detected in the environment. The topology will appear only when you have OT devices and you have enabled this Controlled-GA feature on your tenant.
-
Flow of traffic from source to destination within these OT devices.

-
Alert generated at specific time stamp. You can click on the alert to see the event log.
-
Graph of information received in bytes per day for the last 10 days.
-
Graph of information sent in bytes per day for the last 10 days.
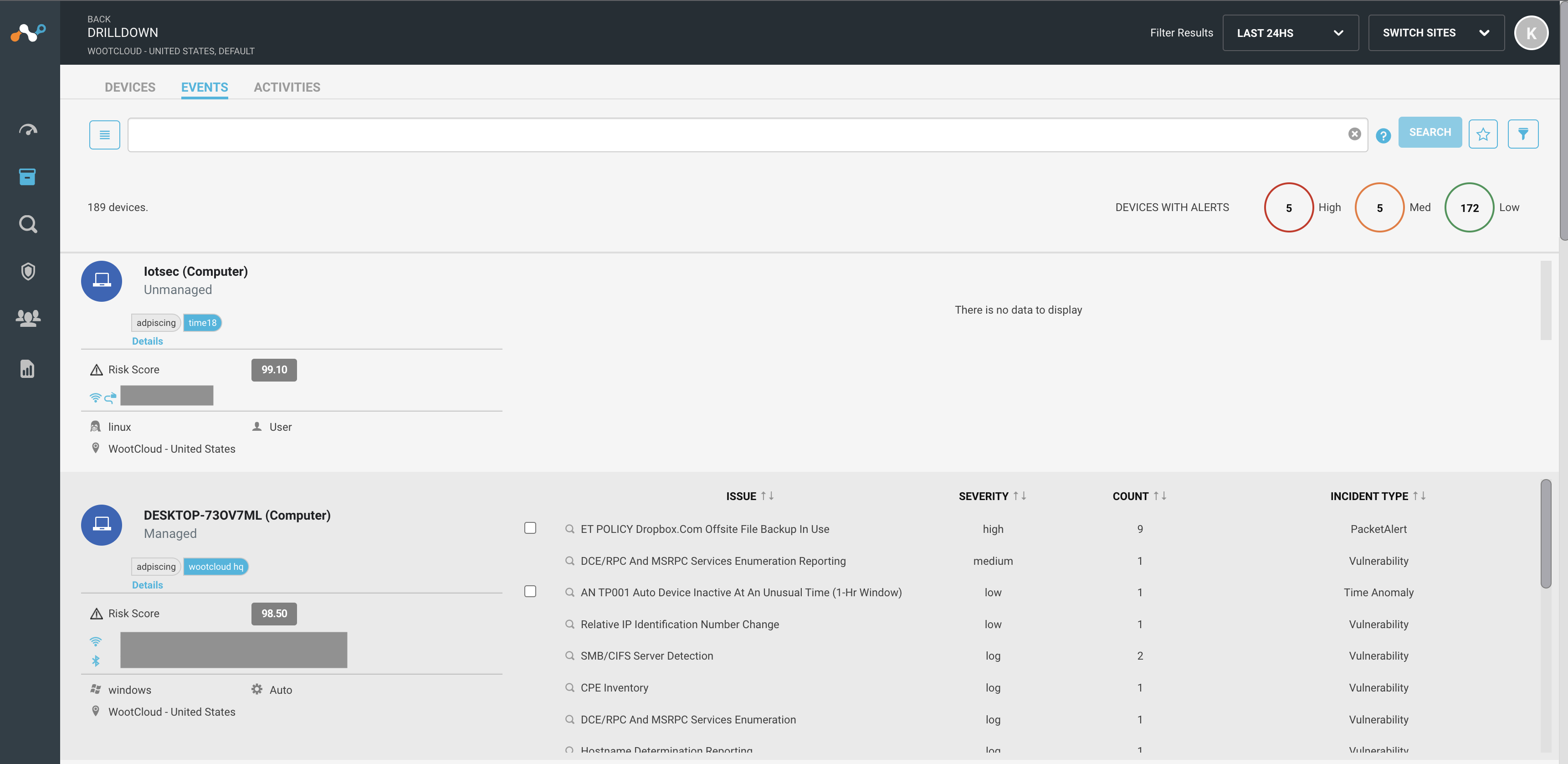
Event View
- You can see the number of devices with risk at the top right chart.
- You can see the host name, type, tags assigned, and managed or unmanaged information.
- Click details link to see the device summary.
- You can see the risk score calculated by Netskope proprietary risk engine, which categorizes packet alerts, device software vulnerabilities and device behavior anomalies into threat vectors.
- It shows if the device is Wi-Fi, wired, or undefined interface connected.
- You can see the operating system and site assigned information. It shows if the device is user or automatically controlled.
- The list of issues with every device is listed in front of the device name. Click on a specific issue for more information of the issue.
When an event such as a Packet Alert incident type occurs, the Event Details page provides rich data regarding the event such as Direction, Payload, 5-Tuple information, etc. It also provides device context regarding Source and Destination devices. Payload decode button in the Event Details page will decode the payload from base64 encoded form to plain user understandable text.

Search and Filter the Inventory
You can filter the details on the screen using advanced and basic filters. On top of the screen, you can find a search bar that filters the device results.
- Advanced filters – allow you to make a query in the database using different parameters. For example,
os = "android"query will show results of devices with android operating systems in the network.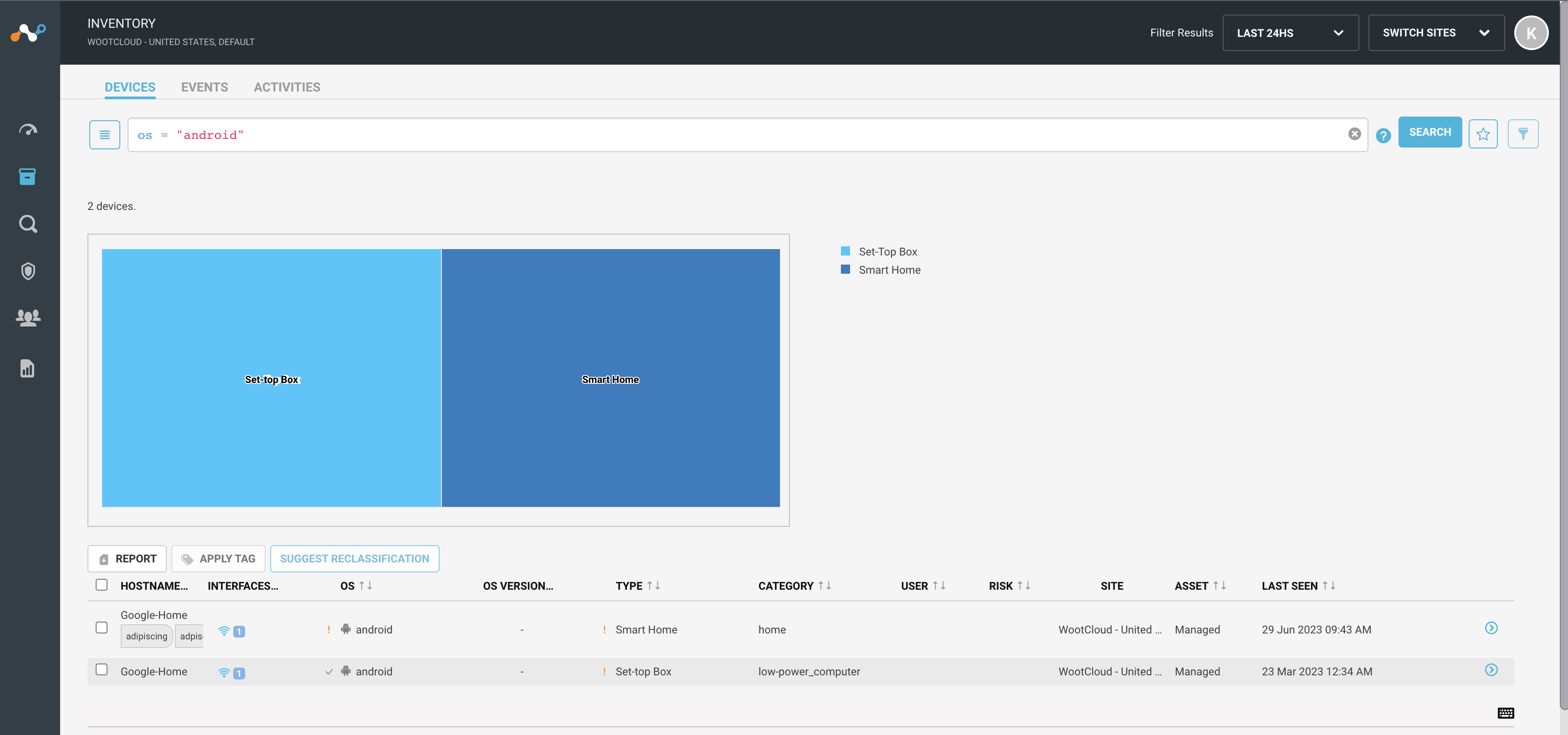
- Basic filters – you see a list of parameters that you can use to filter the device results on the page. You can select the parameters from the list. For example, selecting the operating system as android will filter results of assets which are using the android operating system. You can select multiple parameters to filter the results at once.
Points to remember
- Click the search button to filter the results using the parameters.
- Click the help icon on the right side of the screen and it shows you some basic formats to use the advanced filter.
- You can clear the search filter using the cross button on the right of the search bar.
- Click on the star icon to save the modified search and later you can see the saved searched in the by pressing the list icon at start of the search bar.