Deploy Client On Android Using Intune
Deploy Client On Android Using Intune
This documents illustrates the procedure to deploy Netskope Client in Android devices using Intune.
Prerequisites
-
In the Netskope UI, go to Settings > Security Cloud Platform > Netskope Client > MDM. Download the Netskope Root and Intermediate Certificate.
-
On the same page locate and save Organization ID token value.
-
User accounts provisioned within MDM/EMM platform must match those provisioned with the Netskope tenant.
Bind Android for Enterprise with Intune
Before you begin, ensure that you have configured Android for Enterprise binding for Microsoft Intune. This is done from the MS Endpoint Manager (https://endpoint.microsoft.com/).
-
Log into the Endpoint Manager admin center, go to Devices > Android and select Android Enrollment.
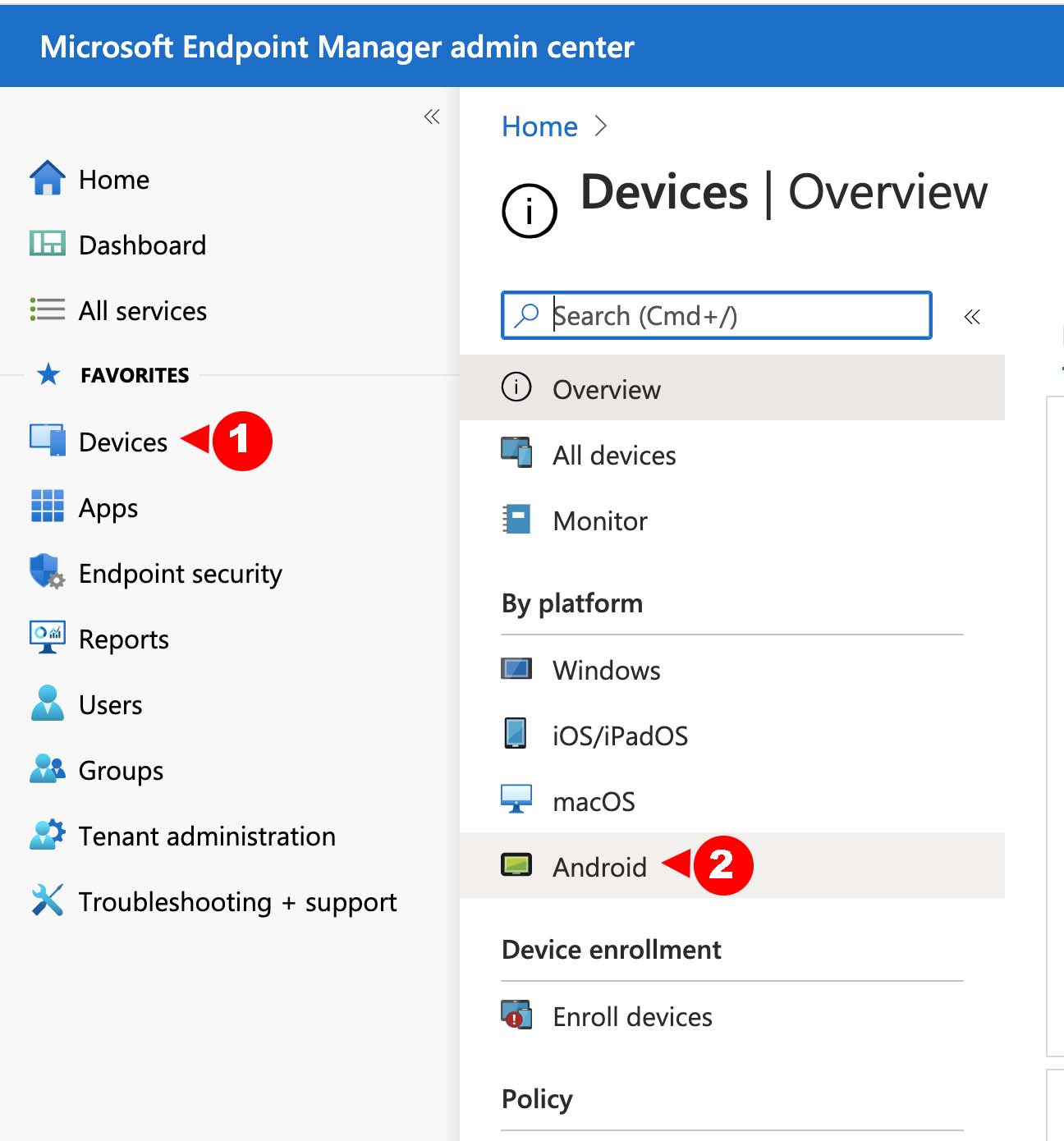
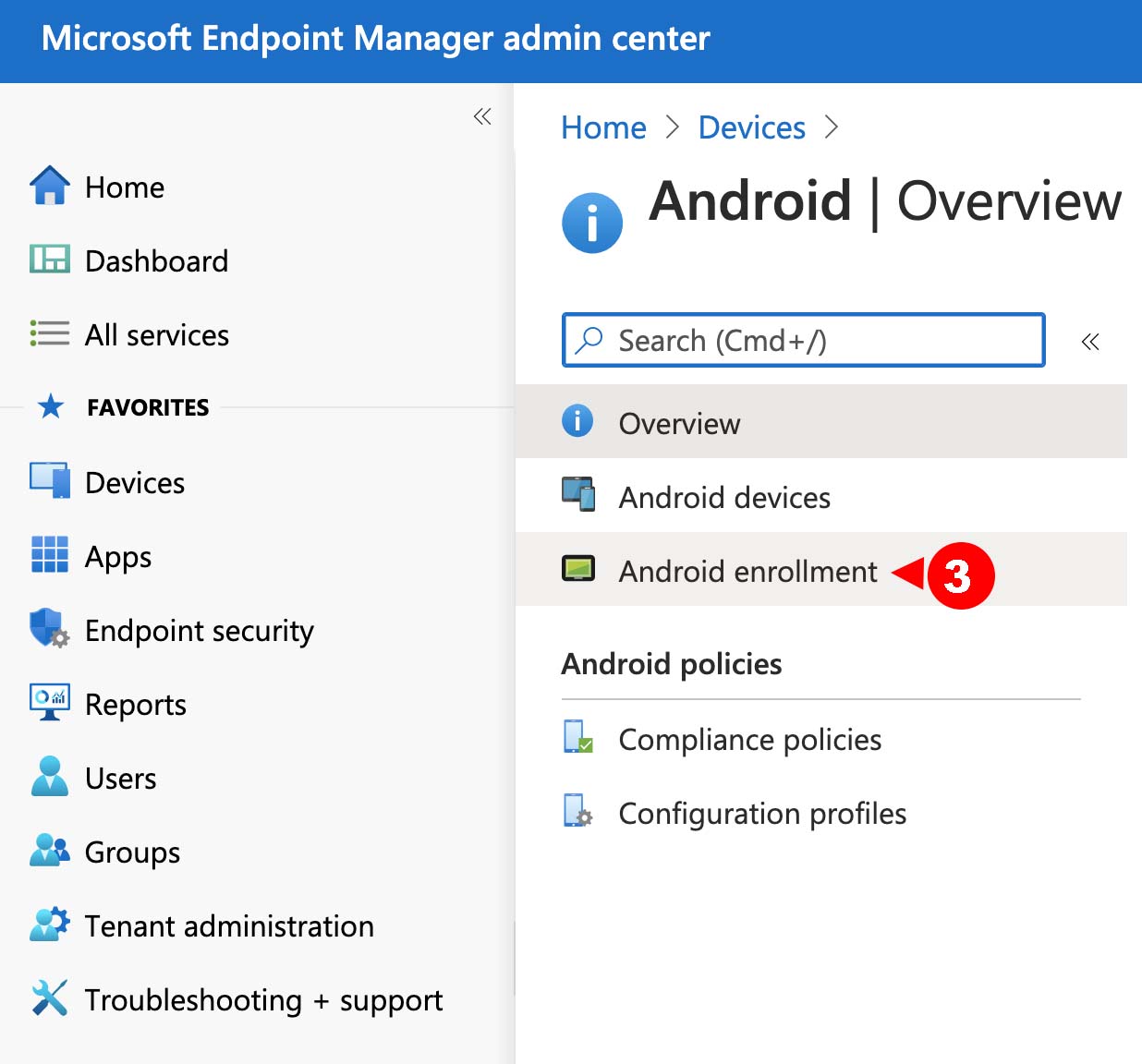
-
Click Managed Google Play.
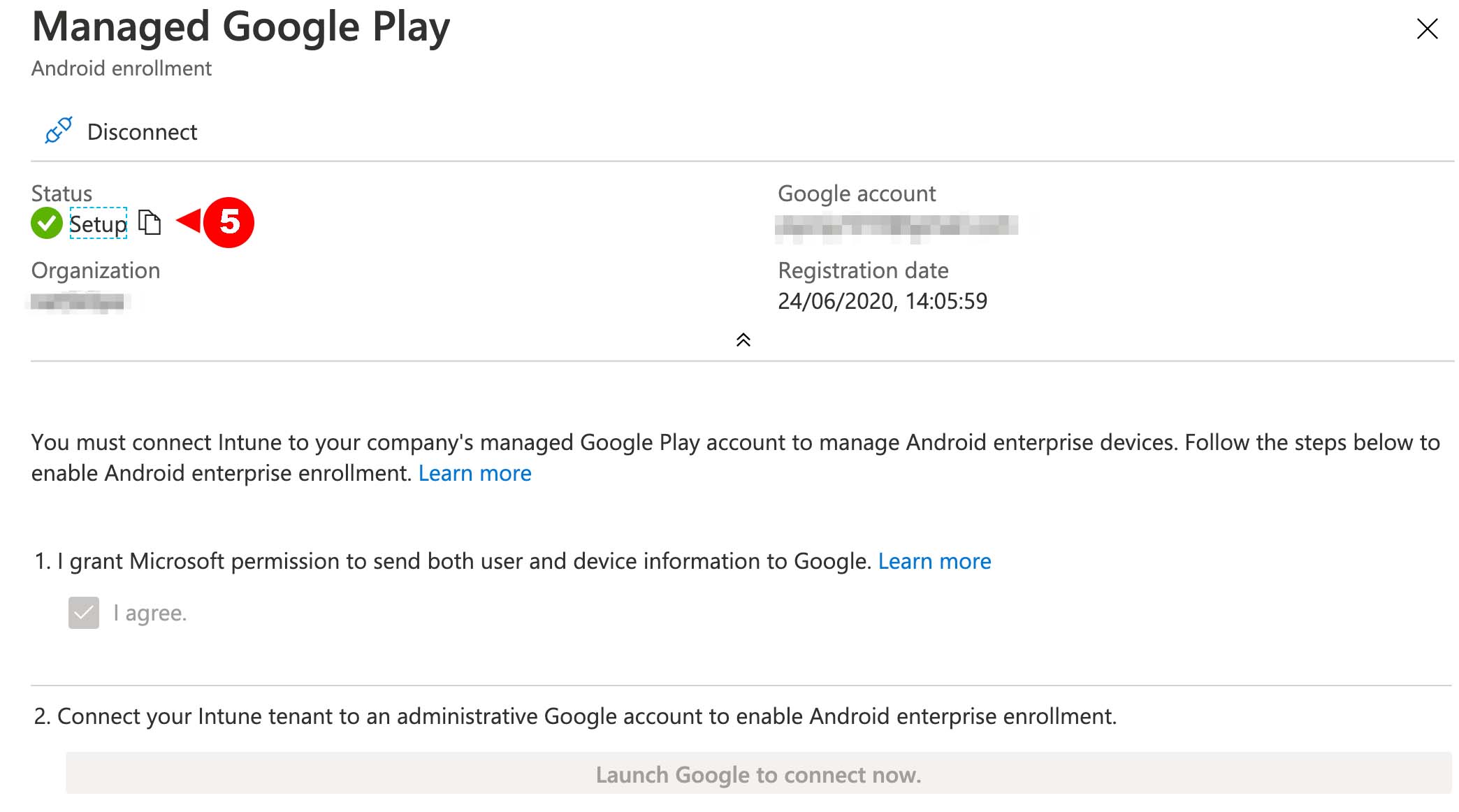
Select the I agree checkbox and click the Launch Google to Connect now button. In the Google Play pop-up window, complete the business registration steps.
-
After registration is complete, go to MS Endpoint Manager admin center, click Devices > Android > Android Enrollment > Managed Google Play to verify the registration process. If successful, the Status label will display Setup with a green tick.
-
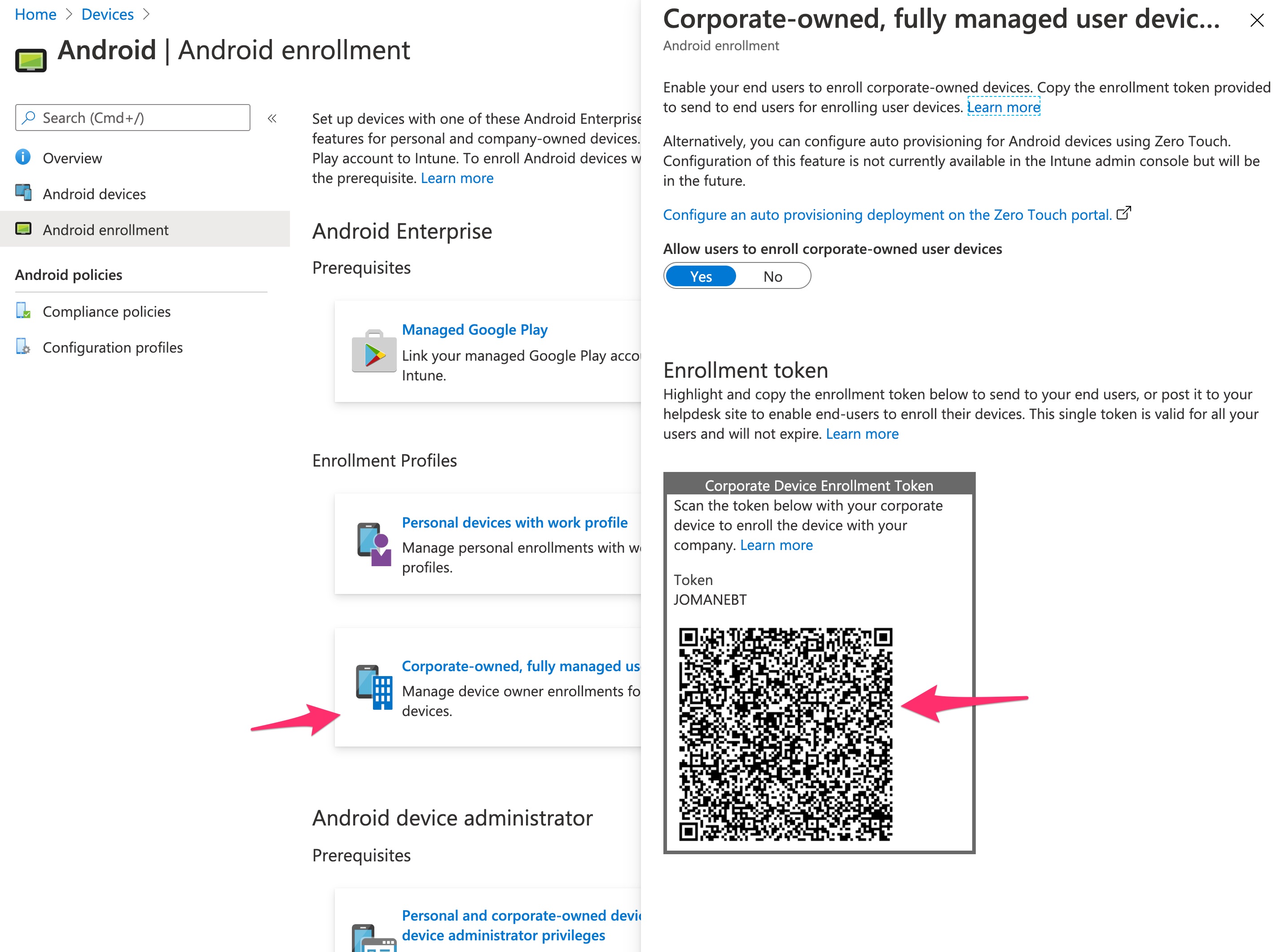
In the Android Enrollment page, select the Enrollment Profile to get the token that you can share with users for enrollment.
Approve Netskope Client
-
Log in to your Google Play Store account and search for Netskope Client.
-
Click Approve send authorization to MS Endpoint Manager.
Setting up Apps in MS Endpoint Manager
-
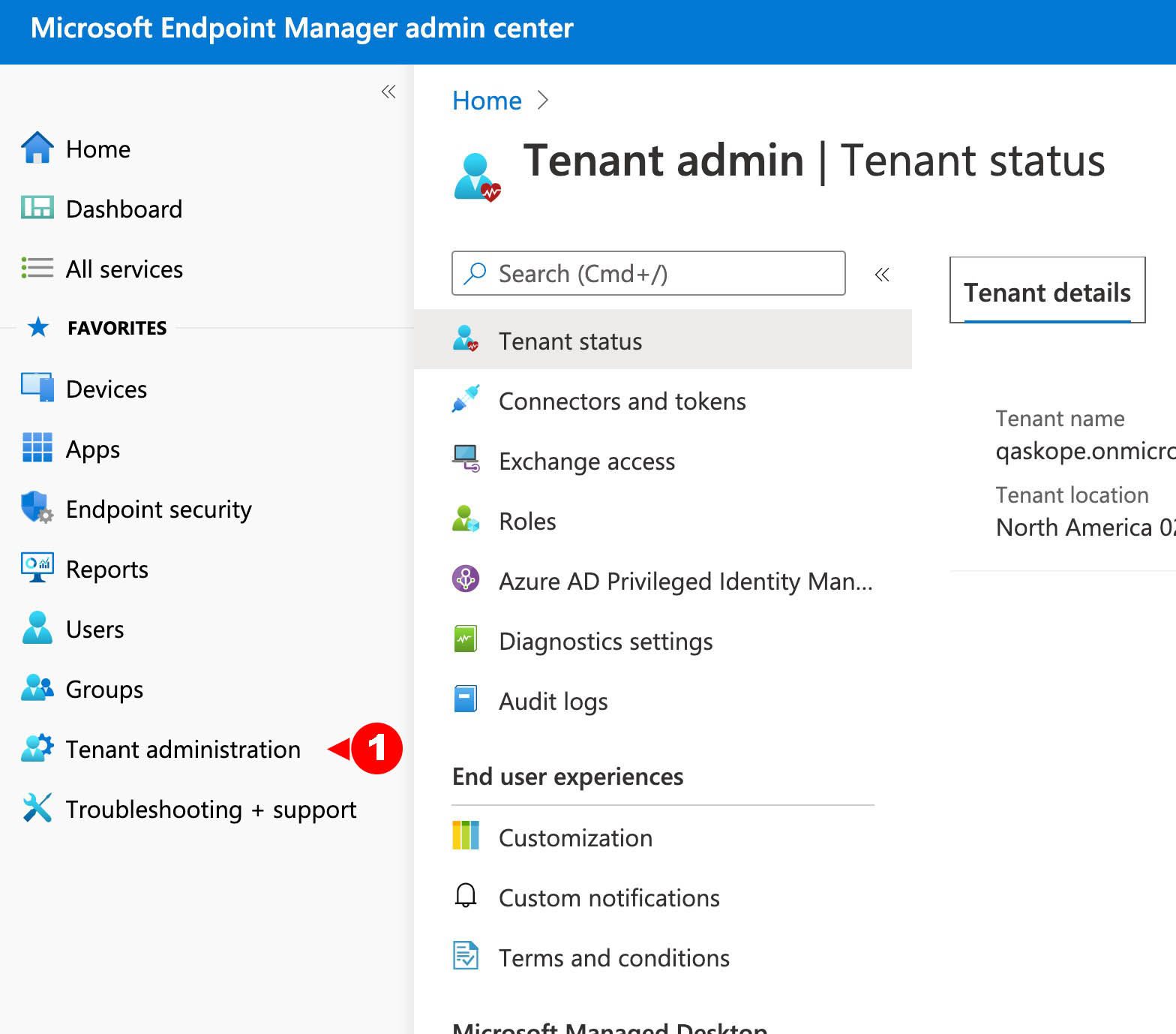
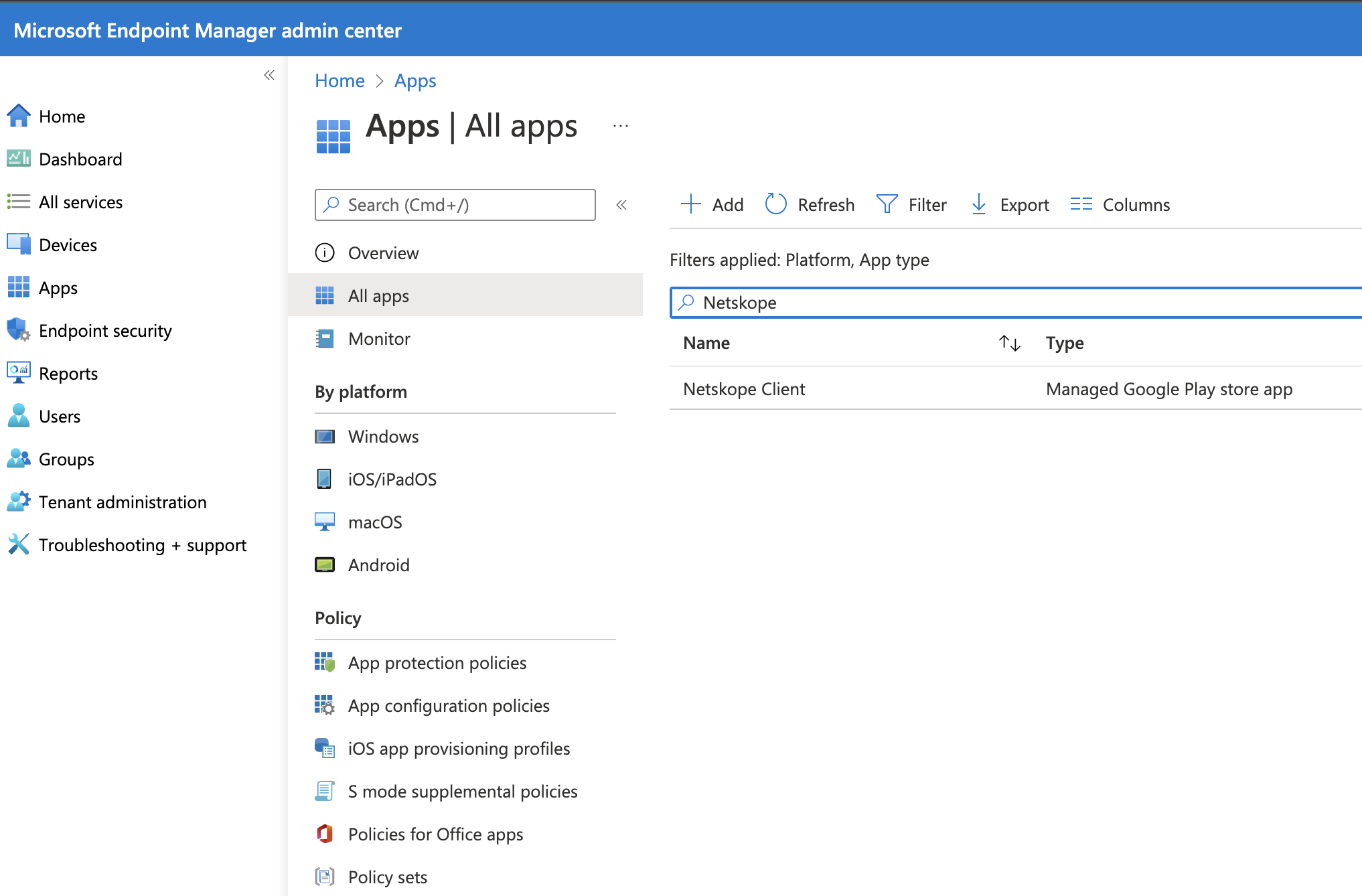
In the MS Endpoint Manager admin center, go to Tenant Administration > Connectors and Token page.
-
Select Managed Google Play and click Sync to get all approved apps listed in Intune Apps > All Apps.
Deploy Netskope Client
Netskope Client can be deployed to users or user groups as an optional or mandatory deployment action.
-
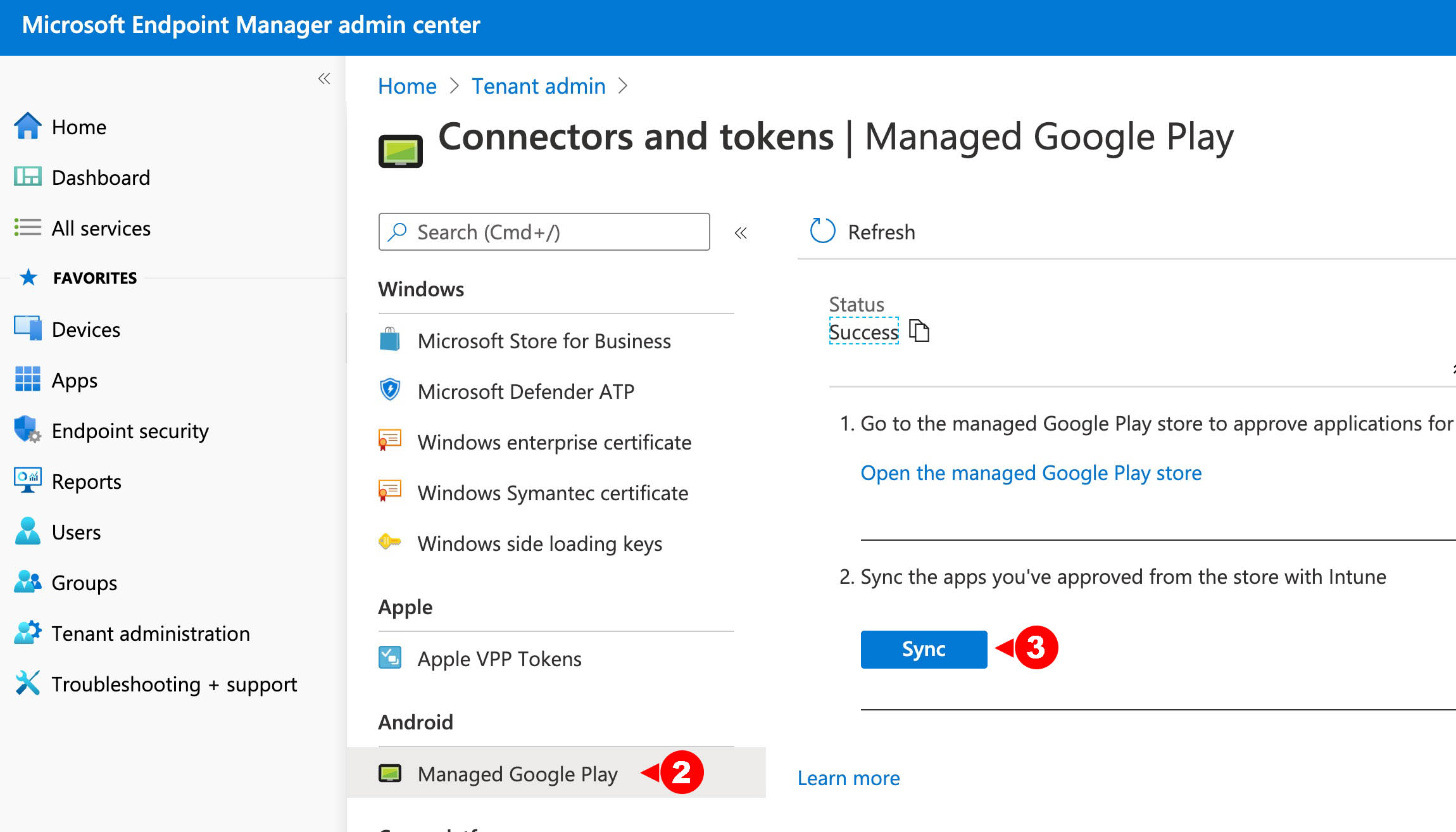
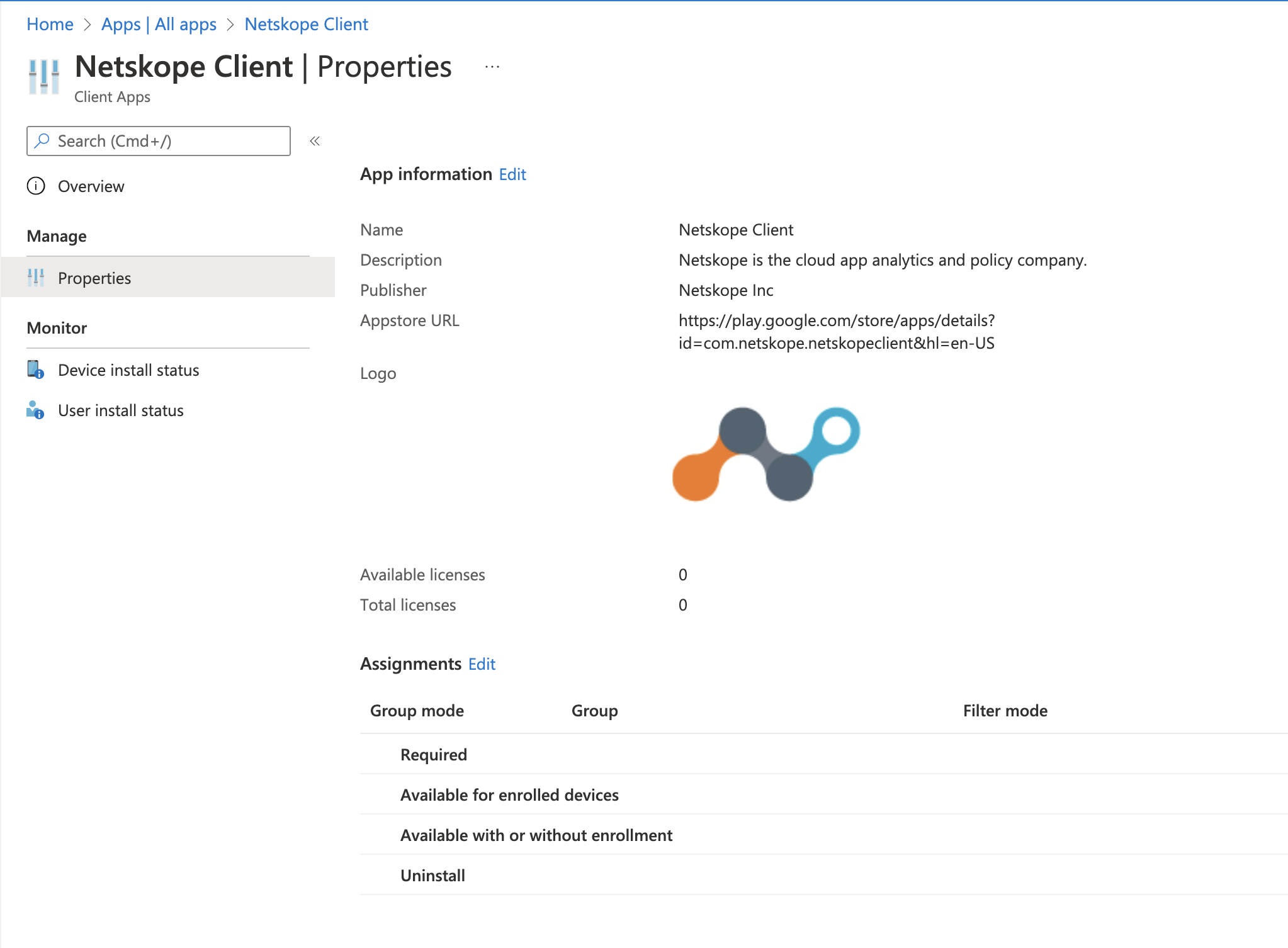
In the MS Endpoint Manager admin console, go to Apps > All Apps and select Netskope Client.
-
Click Properties and then click Assignments.
-
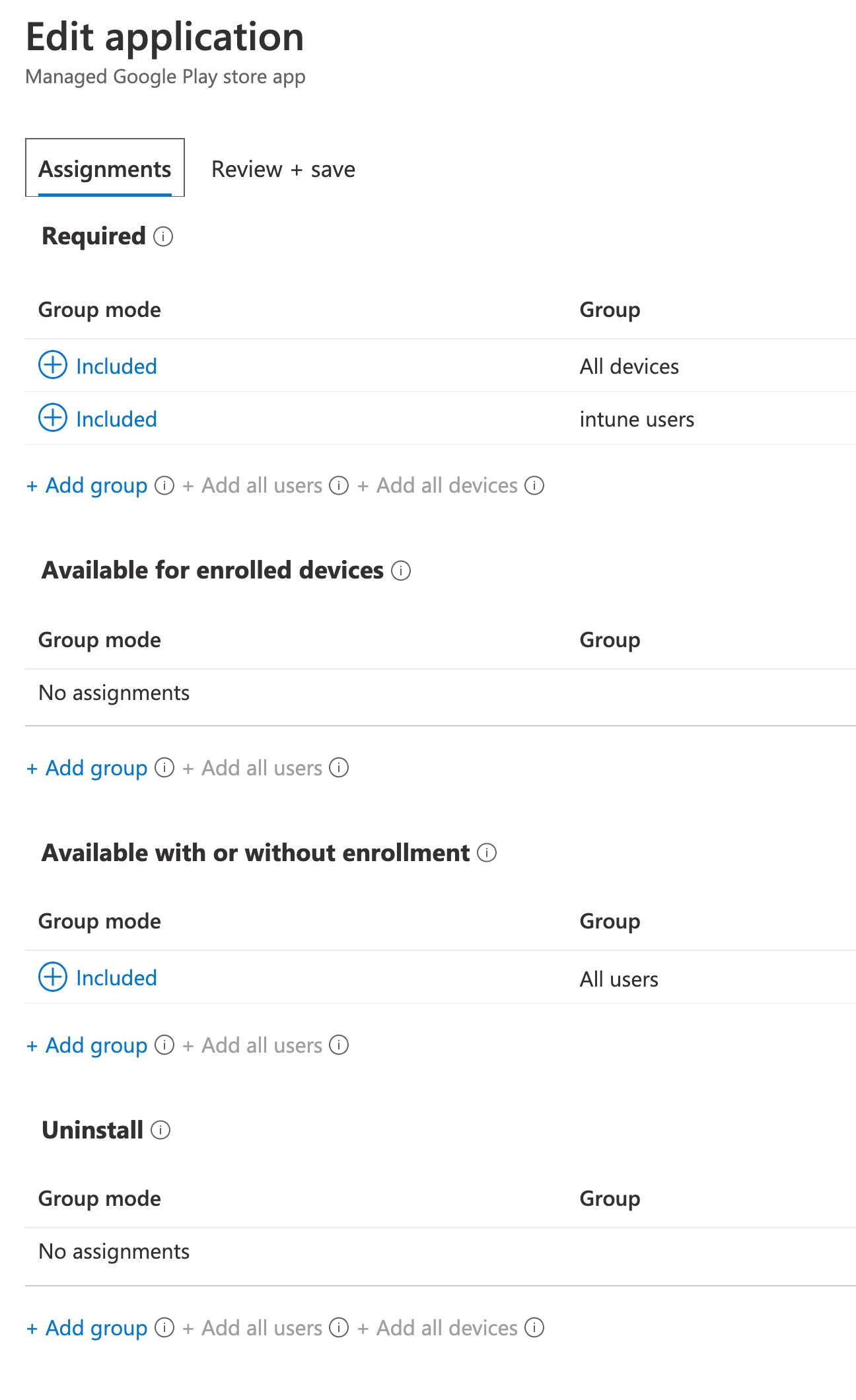
Select the user groups or users to which the app is to be deployed in the Required section (options +Add group, +Add all users, +Add all devices) and click Review+Save, and then click Save.
-
Select the appropriate deployment action and click Save.
Create App Configuration and Deploy
-
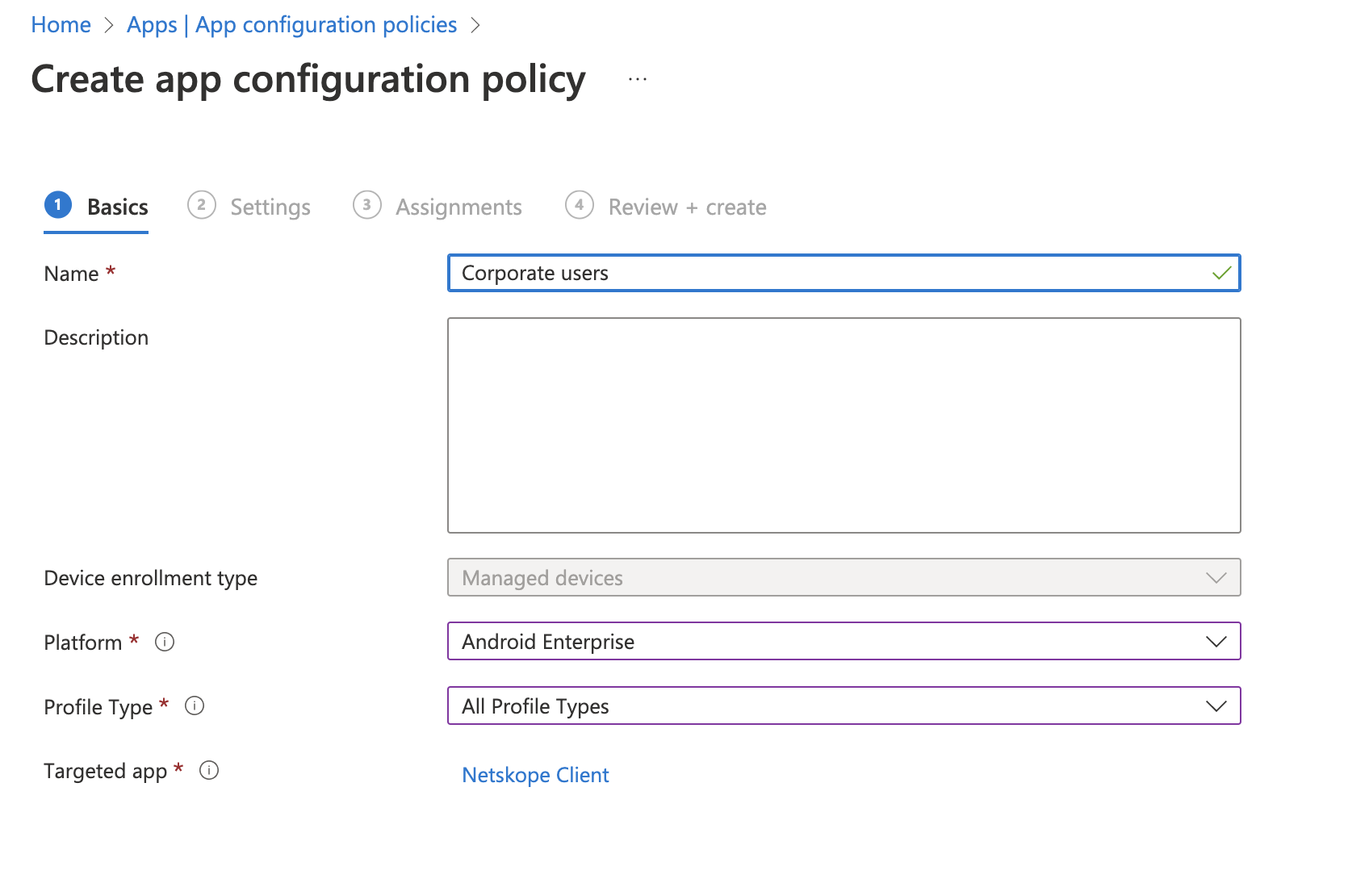
In the MS Endpoint Manager admin center, go to Apps > App Configuration Policy and click + Add and select Managed Devices.
-
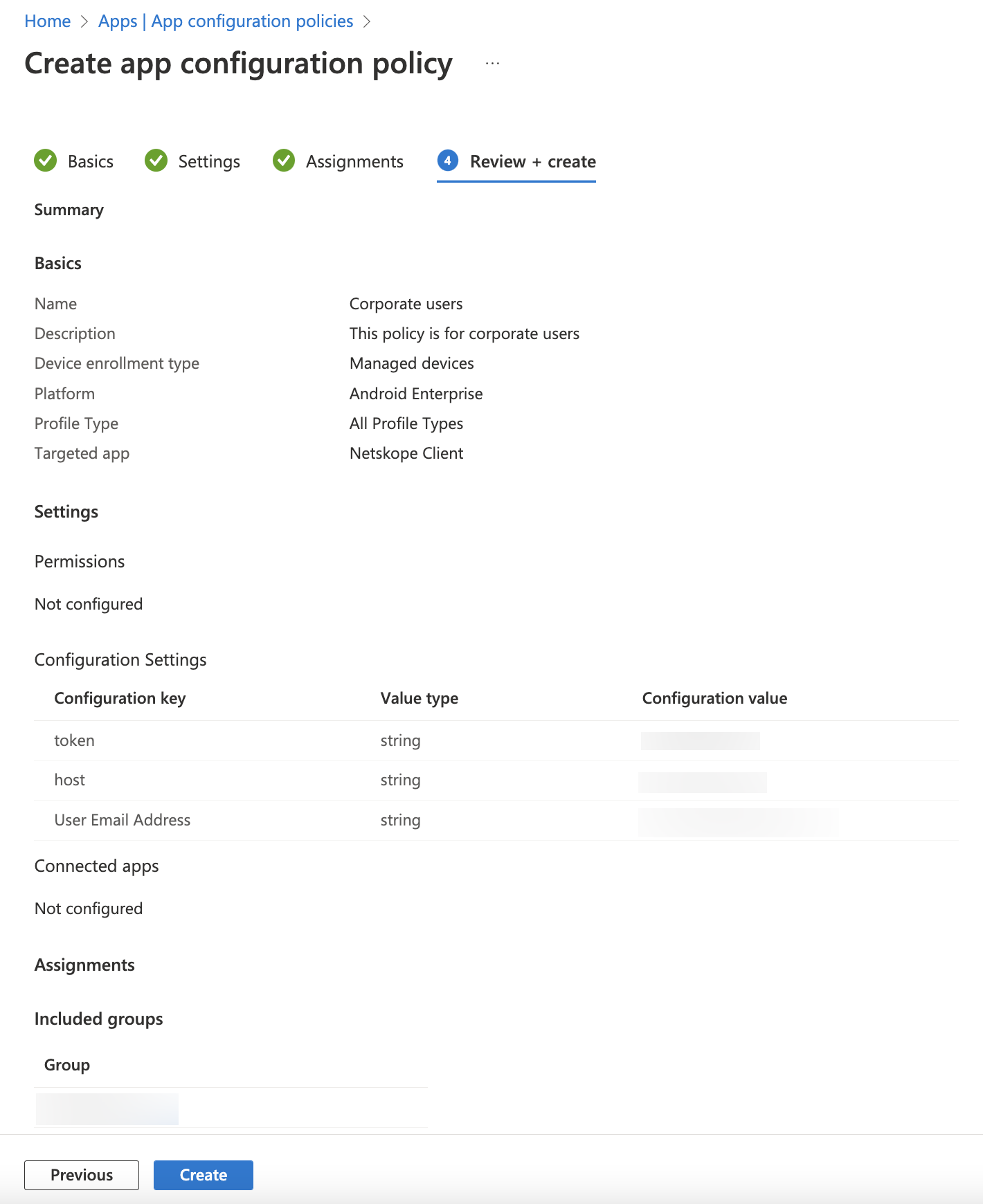
In the Basics section of the Create app configuration policy page, enter the following details and click Next.
-
Name: Give a name to the policy.
-
Platform: Android Enterprise
-
Associated App: Select Netskope Client
-
-
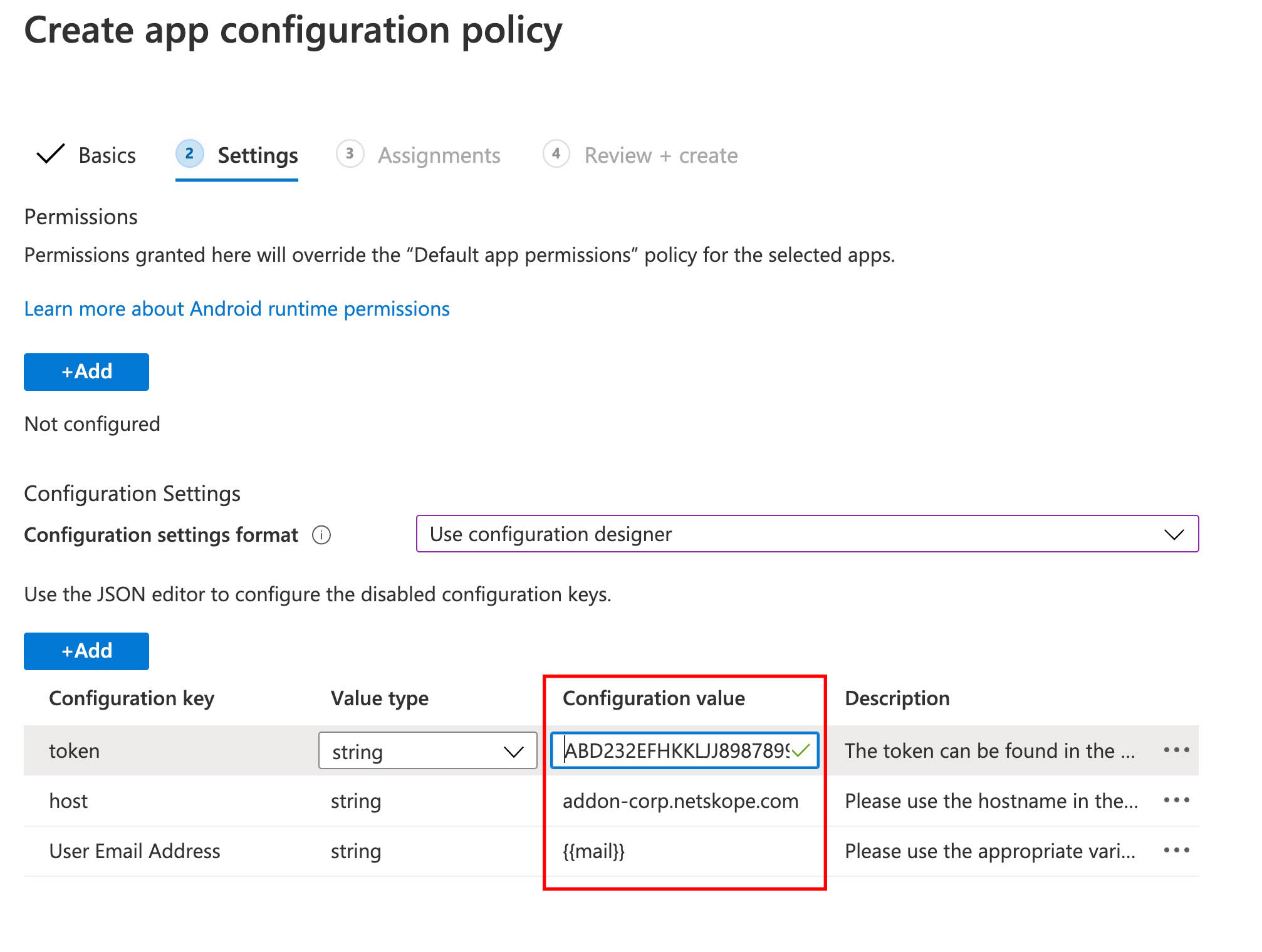
In the Settings section of the Create app configuration policy page, locate Configuration Settings and select the Use configuration designer option from the Configuration settings format dropdown list.
-
Click Add and select the following mandatory values and click OK.
-
User Email Address: {{mail}}
-
For environments where user context is not available (i.e. shared devices, kiosks) static email addresses should be used. This email should match provisioned user account email in Netskope tenant
-
-
Host: <addon-<tenant-URL>
-
Token: <Organization Key>
 Locating Your Organization ID
Locating Your Organization ID
The Organization ID is case-sensitive.
– Login to your tenant with admin credentials.
– Click Settings > Security Cloud Platform > MDM Distribution.
– In the MDM Distribution page, scroll down to Create VPN Configuration section to find your Organization ID.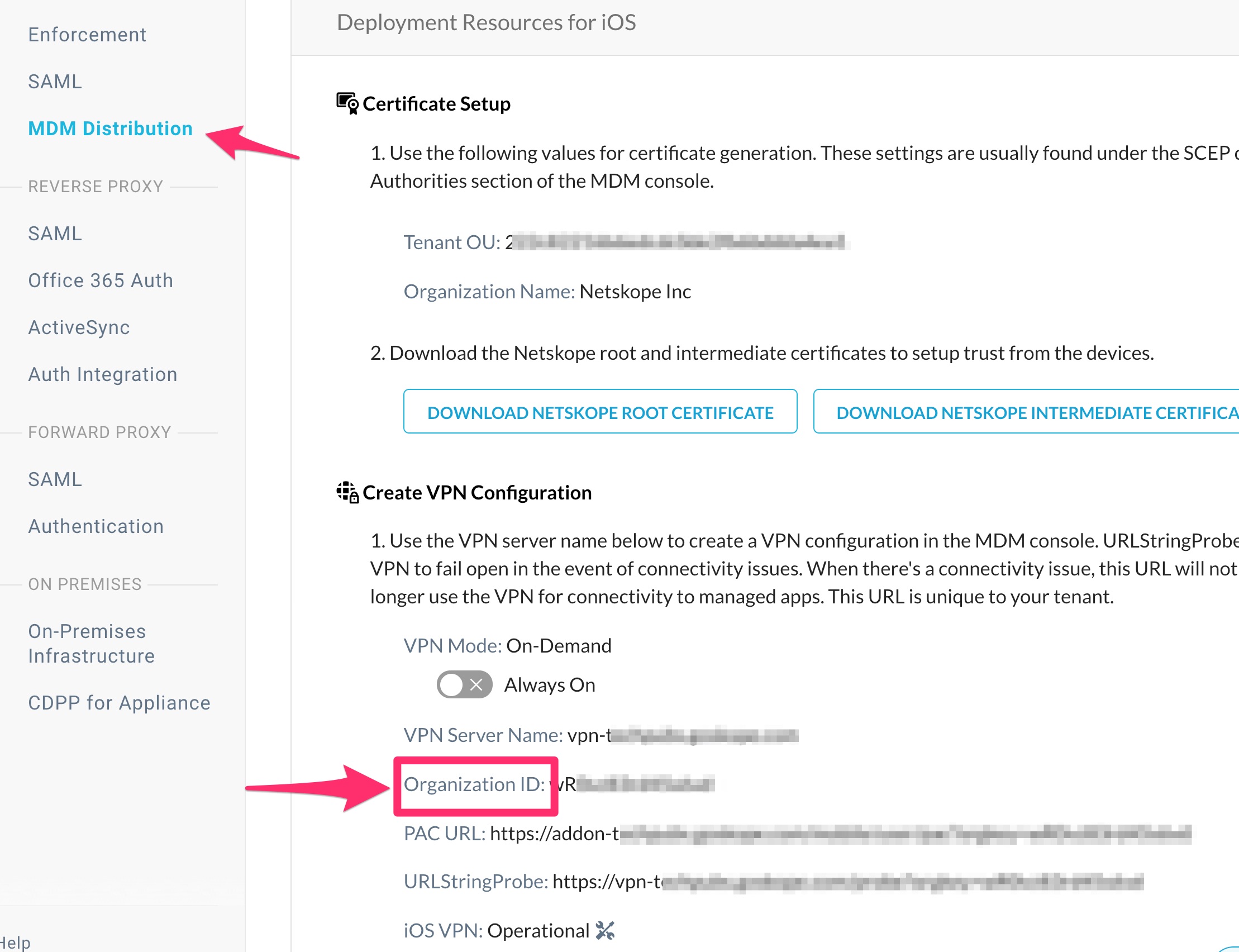
– ns_mdm_check is an optional value that is used for Android device classification purposes. If you are not doing device classification for Android, you can safely ignore this field. -
-
-
In the Assignments section of the Create app configuration policy page, select groups from the Assign to dropdown menu to which the policy is applied. Assuming the option selected was Selected Groups, select include the Microsoft Entra ID groups that this policy will apply to and click Next.
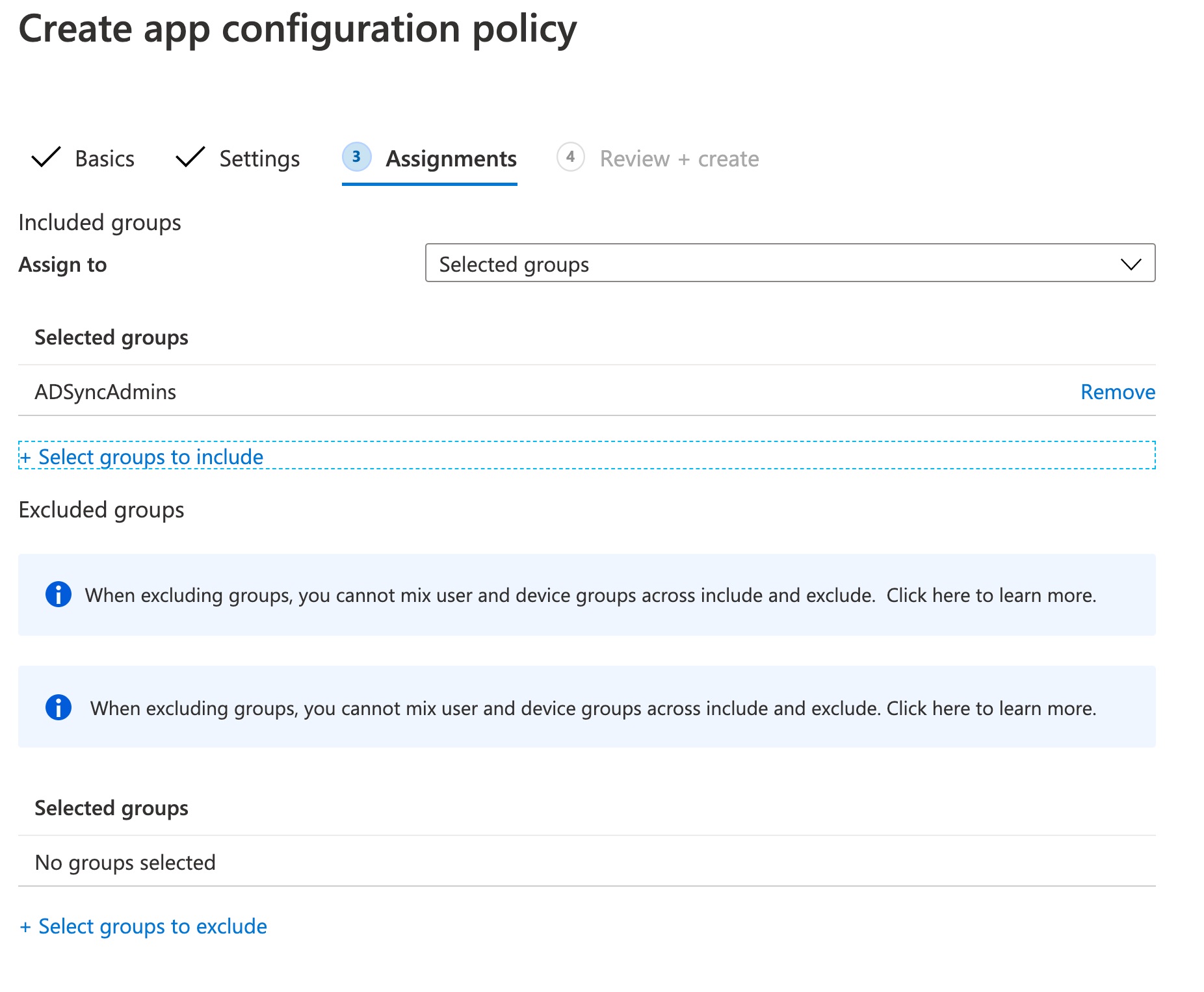 You can also select groups that can be excluded from this configuration policy.
You can also select groups that can be excluded from this configuration policy. -
In the Review + create section of the Create app configuration policy page, review the configuration and click Create.
-
Enroll the Android devices to the Intune Company Portal application available on Google Play.
Enable Zero-touch Enrollment
The following steps enable zero-touch enrollment of Android devices with Microsoft Intune after the deployment of NS Client. This also enables SSL inspection with the presence of the trusted CA certificates in the user store.
-
Create VPN Configuration Profile
-
Create Trusted Netskope Root Certificate Profile
-
Create Device Restrictions Profile
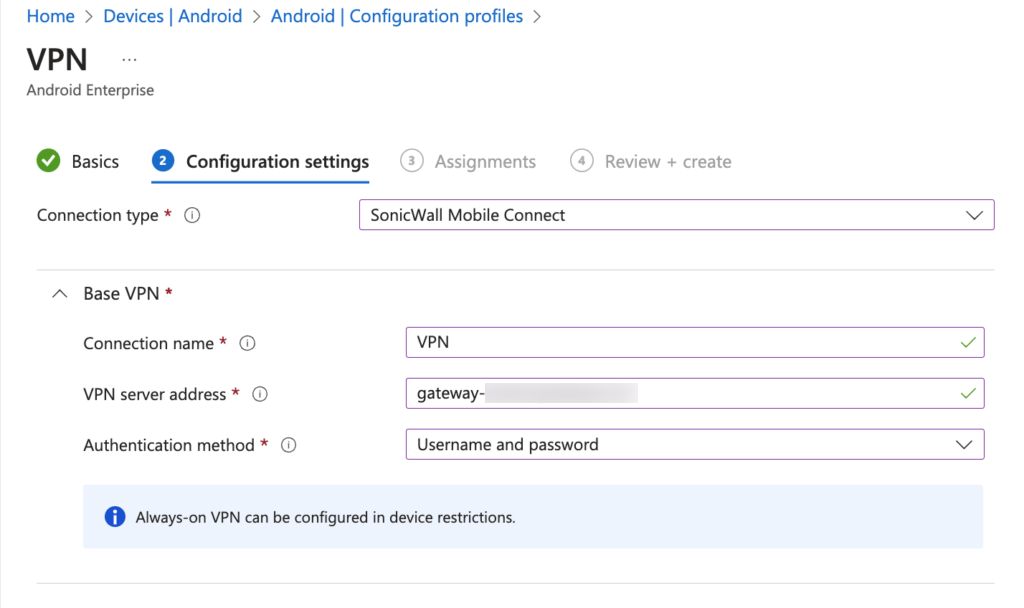
Create VPN Configuration Profile
Here, you can add the VPN profile in Intune instead of making Netskope Client assess it. To learn more, view Create Profile.
To create a VPN Profile:
-
Go to Devices > Android > Configuration Profiles > Create Profile.
-
In Create a Profile, select the following:
-
Platform: Android Enterprise
-
Profile Type: VPN
-
-
Click Create.
-
In Basics, enter a descriptive name for the profile and click Next.
-
In Configuration settings, choose the Connection Type as SonicWall Mobile Connect.
-
After you select the connection type, do the following:
-
Assign the appropriate user/device groups and click Next.
-
Review the configuration and click Create.
Create a Trusted Netskope Root Certificate Profile
Download the Netskope Root and intermediate certificates from the Netskope UI to complete these steps. To get the certificate, go to Settings > Security Cloud Platform > Netskope Client > MDM Distribution.
To create a trusted Netskope certificate profile:
-
In Intune UI proceed to Devices > Android > Configuration profiles.
-
Click Profile > Create Profile. Enter and select these parameters:
-
Name: Enter a unique name.
-
Platform: Android Enterprise
-
Profile type: Trusted certificate
-
-
In the Trusted Certificate panel, provide a name in the Basics tab and click Next.
-
In the Configurations settings tab, upload the Netskope Root certificate.
-
Review your settings, and click Create.
Create Device Restriction Profile
Adding a device restriction profile helps administrators to set policies to control and manage Android devices in their organization. To learn more, view Device Restriction.
To add a device restriction profile:
-
Go to Devices > Android > Configuration Profiles > Create Profile.
-
In Create a Profile, select the following:
-
Platform: Android Enterprise
-
Profile Type: Device Restrictions
-
-
Click Create.
-
In Basics, enter a descriptive name for the profile and click Next.
-
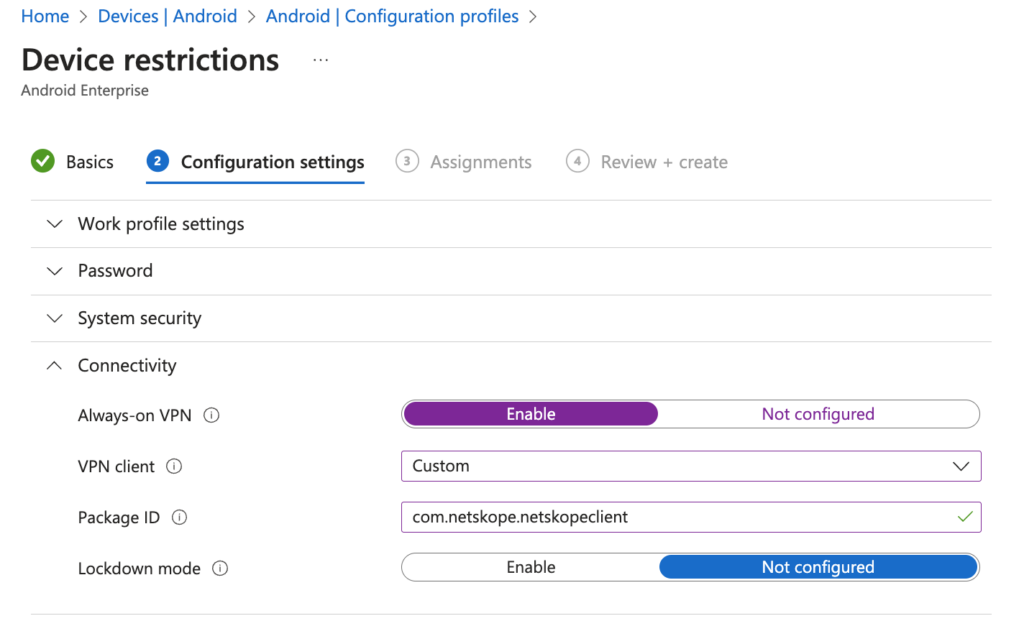
In Configuration settings, expand Connectivity and enter the following:
-
Always-On VPN: Toggle Enable to select this option.
-
VPN Client: Select Custom.
-
Package ID: com.netskope.netskopeclient
-
Lockdown mode: Toggle Not configured to select this option.
-
-
Click Next.
-
Add the appropriate profile assignments and click Next.
-
Review the configuration and click Create.
Enrollment Workflow
After the deployment is complete, Netskpe Client can enroll silently(assuming the enrollment data is correct and is matching the user information provisioned in the tenant). The VPN profile serves as the binding mechanism between source mobile applications and Netskope Client as secure connectivity provider.