AWS GuardDuty Plugin for Threat Exchange
AWS GuardDuty Plugin for Threat Exchange
This document explains how to configure the AWS GuardDuty integration with the Cloud Threat Exchange module of the Netskope Cloud Exchange platform. This plugin fetches URLs (IPv4 and Domain) and Hash (SHA256) from the AWS GuardDuty platform. This plugin does not support pushing indicators to AWS GuardDuty.
Prerequisites
To complete this configuration, you need:
- A Netskope tenant (or multiple, for example, production and development/test instances) that is already configured in Cloud Exchange.
- A Netskope Threat prevention subscription for malicious file hash sharing.
- A Netskope Cloud Exchange tenant with the Threat Exchange module already configured.
- Access to your AWS Access Key ID (Public Key), AWS Secret Access Key (Private Key), AWS Session Token (Optional, only for temporary user), Region Name, and Detector ID (Unique Detector ID).
AWS GuardDuty Plugin Support
| Fetched indicator types | URLs (IPv4 and Domain), SHA256 |
| Shared indicator types | None |
Mappings
Severity Mapping
| Netskope Severity | AWS GuardDuty Severity |
| <1 | Unknown |
| 1.0 – 3.9 | Low |
| 4.0 – 6.9 | Medium |
| 7.0 – 8.9 | High |
| 9.0 – 10.0 | Critical |
Mappings for Pull (Netskope field – AWS GuardDuty fields)
| Netskope Cloud Exchange indicator Field | AWS GuardDuty Field |
| value |
EbsVolumeScanDetails Mapping NetworkConnectionAction Mapping Service.Action.NetworkConnectionAction.RemoteIpDetails.IpAddressV4 PortProbeAction Mapping Service.Action.PortProbeAction.PortProbeDetails.RemoteIpDetails.IpAddressV4 DnsRequestAction Mapping Service.Action.DnsRequestAction.Domain |
| type |
EbsVolumeScanDetails Mapping NetworkConnectionAction Mapping
URL DnsRequestAction Mapping URL |
| firstSeen |
EbsVolumeScanDetails Mapping NetworkConnectionAction Mapping Service.Action.EventFirstSeen PortProbeAction Mapping Service.Action.EventFirstSeen DnsRequestAction Mapping Service.Action.EventFirstSeen |
| lastSeen |
EbsVolumeScanDetails Mapping NetworkConnectionAction Mapping PortProbeAction Mapping Service.Action.EventLastSeen DnsRequestAction Mapping Service.Action.EventLastSeen |
| severity |
EbsVolumeScanDetails Mapping NetworkConnectionAction Mapping Severity PortProbeAction Mapping Severity DnsRequestAction Mapping Severity |
| tags |
EbsVolumeScanDetails Mapping GuardDuty-private if PrivateIpAddress is present in NetworkInterfaces NetworkConnectionAction.Blocked=<value> + GuardDuty-public if PublicIp is present in NetworkInterfaces + GuardDuty-private if PrivateIpAddress is present in NetworkInterfaces PortProbeAction Mapping DnsRequestAction Mapping |
| comments |
EbsVolumeScanDetails Mapping Filepath:Service.EbsVolumeScanDetails.ScanDetections.ThreatDetectedByName.ThreatNames.FilePaths.FilePath,Description:Description
PortProbeAction Mapping DnsRequestAction Mapping |
Permissions
Below are the permissions needed to be attached to the IAM user for the plugin workflow.
- GetFindings
- ListFindings
API Details
List of APIs Used
This plugin uses python (Boto3 v1.34.44) library to get findings from the AWS GuardDuty platform.
Library: The AWS SDK for python (Boto3 v1.34.44)
Usage: The AWS SDK for python (Boto3) to create, configure, and manage AWS services,
such as Amazon Elastic Compute Cloud (Amazon EC2) and Amazon Simple Storage Service
Creating a GuardDuty Client Object
guardduty_client = boto3.Session(
aws_access_key_id=self.aws_public_key,
aws_secret_access_key=self.aws_private_key,
region_name=self.configuration["region_name"].strip()
config=Config(proxies=self.proxy, user_agent=self.useragent),
).client("guardduty")
List Findings
findings = guardduty_client.list_findings(
DetectorId=detection_id,
MaxResults=1,
SortCriteria={"AttributeName": "updatedAt", "OrderBy": "ASC"},
)
List Findings with Pagination
paginator = guardduty_client.get_paginator("list_findings")
page_iterator = paginator.paginate(
DetectorId=self.configuration["aws_detector_id"].strip(),
FindingCriteria={
"Criterion": {
"updatedAt": {
"Gte": int(checkpoint.timestamp() * 1000),
}
}
},
SortCriteria={"AttributeName": "updatedAt", "OrderBy": "ASC"},
)
Get Findings
guardduty_client.get_findings(
DetectorId=detection_id,
FindingIds=finding_ids,
)
Performance Matrix
This plugin has been tested by fetching 288 findings from AWS GuardDuty Platform it takes around 15 seconds to fetch and store indicators from these findings in Netskope CE
|
Stack details |
Size: Large
RAM: 32 GB CPU: 16 Cores |
|
Indicators fetched from AWS GuardDuty |
~ 1K per minute |
| Indicators shared to AWS GuardDuty |
NA |
User Agent
- netskope-ce-5.0.0-cte-aws-guardduty-v1.1.0
Workflow
- Get your AWS GuardDuty credentials.
- Configure the AWS GuardDuty plugin.
- Configure sharing between Netskope and AWS GuardDuty.
- Validate the AWS GuardDuty Plugin.
Click play to watch a video.
Create a Policy for AWS GuardDuty
- Go to IAM Services in the AWS Console.
- Click Create policies.
- Select GuardDuty in Services.

- Select GetFindings and ListFindings.
- Click Next.
- Add a Policy Name.

- Click Create Policy.

Plugin Authentication Methods
IAM Role Anywhere Configuration
Prerequisites
The AWS Certificate Manager service is required to be enabled to authenticate the plugin using the AWS IAM Roles Anywhere Authentication Method.
Note: Make sure you create the Private Certificate Authority, Trust Anchor, and Profile in the same region in which your AWS S3 Source Bucket resides.
Create an IAM Policy
This Policy contains the required permissions for creating a Private CA Certificate (including Permissions for creating a Trust Anchor and Profile) and using IAM Roles Anywhere.
- Go to Policy Generator and click Add Statement to generate a policy.
- Select Type of Policy: IAM Policy
- Effect: Allow
- AWS Service: AWS Private Certificate Authority
- Actions:
- CreateCertificateAuthority
- DescribeCertificateAuthority
- GetCertificate
- GetCertificateAuthorityCertificate
- GetCertificateAuthorityCsr
- ImportCertificateAuthorityCertificate
- IssueCertificate
- ListCertificateAuthorities
- ARN: *
- Click Add Statement.

- Select Type of Policy: IAM Policy
- Effect: Allow
- AWS Service: AWS Identity and Access Management (IAM)
- Actions:
- AttachRolePolicy
- CreateAccessKey
- CreateRole
- DeleteRole
- PassRole
- ARN: *
- Click Add Statement.

- Select Type of Policy: IAM Policy
- Effect: Allow
- AWS Service: AWS Certificate Manager
- Actions:
- DescribeCertificate
- ExportCertificate
- GetCertificate
- ListCertificates
- ListTagsForCertificate
- RequestCertificate
- ARN: *
- Click Add Statement.

- Select Type of Policy: IAM Policy
- Effect: Allow
- AWS Service: AWS Identity and Access Management Roles Anywhere
- Actions:
- CreateProfile
- CreateTrustAnchor
- GetProfile
- GetTrustAnchor
- ListProfiles
- ListTrustAnchors
- ARN: *
- Click Add Statement.

- Click Generate Policy.

- Copy the Policy as it is used in the next step for creating the policy required for creating the Private CA certificates.
- Go to the AWS Console and select IAM from All Services. Click Policies from the left panel, and click Create Policy.

- Copy the policy to the JSON tab, and then click on Next: Tags and Next: Review.
- Enter a name, like netskope-ce-rolesAnywhere-policy, and click Save Changes.

Create a Private Certificate Authority
- Log in to AWS Console.
- Search for Certificate Manager.

- Click AWS Private CA.
- Click Create a private CA.

- Select General-purpose for Mode Options.
- Select Root for CA type options.

- Enter the Organization (O).

- Select RSA 2048 for Key algorithm options.


- Add tags if any (optional).
- Enable the checkbox in the CA permissions options section.
- Enable the checkbox in the Pricing section.
- Click Create to create the CA certificate.


- From Actions, select Install.

- Click Confirm and Install.


Create a Trust Anchor
- Search for the IAM service, and go to Roles under Access management. Scroll down to Roles Anywhere and select Manage.

- Click Create a Trust anchor.

- Enter the Trust anchor name, like netskope-ce-trust-anchor.

- Select AWS Certificate Manager Private CA (created in the previous steps) as a Certificate authority (CA) source
- Add tags if required.
- Click Create a trust anchor.


- Click on the created Trust Anchor and copy the Trust Anchor ARN.

Create an IAM Role
- Go to IAM services in the AWS Console.
- Click Role under Access management.
- Click Create Role.

- For the Trusted entity type, select Custom Trust Policy.

- Go to Policy Generator.
- Replace the Custom trust Policy with the below Trust Policy; this policy contains the permissions for using the roles anywhere service:
{ "Version": "2012-10-17", "Statement": [ { "Effect": "Allow", "Principal": { "Service": [ "rolesanywhere.amazonaws.com" ] }, "Action": [ "sts:AssumeRole", "sts:TagSession", "sts:SetSourceIdentity" ] } ] } - Click Next.
- In the Permissions policies, select the previously created Bucket Policy.

- Click Next.
- Provide a Role name, like netskope-ce-roleAnywhere, and add a Description for the role.
- Click Create role.

- Make a note of the Role ARN as this will be required in the Plugin configuration parameter: Role ARN for the authentication method AWS IAM Roles Anywhere.


Create a Profile
- Select Roles under Access management.
- Scroll down to Roles Anywhere and click Manage.

- Expand the Setup steps.
- Click Step 2: Configure roles.
- Click Configure a profile.

- Enter a Profile name, like netskope-ce-profile.
- Select the role created in Create IAM Role section: netskope-ce-roleAnywhere.

- Remove the Inline Policy.
- Click Create profile.



- Click on the created Profile and copy the Profile ARN.

Request a Private Certificate
- Go to AWS Certificate Manager > Request certificate.
- Select Request a private certificate.

- Click Next.
- Select the Certificate authority created in the previous steps.

- Provide a domain name in the Fully qualified domain name field, like netskope-ce.com.
- Select RSA 2048 for the Key algorithm.

- Add tags if required.
- Acknowledge the Certificate renewal permissions.
- Click Request.

- Go to List certificates from the navigation pane of AWS Certificate Manager.
- Select the certificate created previously.

- Click Export.

- Enter the passphrase. Make a note of the passphrase as it will be required for the Configuration of the AWS S3 Plugin using the AWS IAM Roles Anywhere Authentication method.
- Click Generate PEM Encoding.

- Download all the Certificates because they won’t be visible again. For new certificates, you will need to Export it again.
 For More Info visit AWS IAM Role Anywhere
For More Info visit AWS IAM Role Anywhere
Deployed on AWS Configuration
Create a Role
- Go to IAM services in the AWS Console.
- Click Create role.

- Select the AWS Service.
- For Use case, select EC2.
- Click Next.

- Select the permission policy created in your Bucket Policy.
- Click Next.

- Enter a Role Name, like netskope-ce-instance-role, and add a Description.
- Click Create Role.

 Note: For this configuration, both Netskope instance and S3 Bucket should be in the same region.
Note: For this configuration, both Netskope instance and S3 Bucket should be in the same region.
Assign a Role to an EC2 Instance
- Open your EC2 instance console.
- Click Instances under Instances.


- Go to Action > Security > Modify IAM Role.

- Select the Role that you created previously (like netskope-ce-instance-role).
- Click Update IAM Role.

Configure the AWS GuardDuty Plugin
- Log in to your CE instance and go to Settings > Plugins.
- Search for and select the AWS GuardDuty plugin box to configure the plugin.

- Enter these values:
- Configuration Name: Unique name for the configuration.
- Sync Interval: Leave default.
- Aging Criteria: Expiry time of the plugin in days. (Default: 90)
- Override Reputation: Set a value to override the reputation of indicators received from this configuration.
- Enable SSL Validation: Enable SSL Certificate validation.
- Use System Proxy: Enable if the proxy is required for communication.

- Click Next.
- Enter these values:
- Authentication Method: Select the method to be used for authentication (Deployed on AWS/AWS IAM Roles Anywhere)
- Private Key: Private Key for decrypting the AWS Private CA Certificate. Required for AWS IAM Roles Anywhere authentication type.
- Certificate Body: Certificate Body for AWS Public/Private CA Certificate. Required for AWS IAM Roles Anywhere authentication type.
- Password Phrase: Password Phrase for decrypting the CA Certificate. Required for AWS IAM Roles Anywhere authentication type.
- Profile ARN: AWS Profile ARN for AWS client authentication. Required for AWS IAM Roles Anywhere authentication type.
- Role ARN: AWS Role ARN for AWS client authentication. Required for AWS IAM Roles Anywhere authentication type.
- Trust Anchor ARN: AWS Trust Anchor ARN for AWS client authentication. Required for AWS IAM Roles Anywhere authentication type.
- Region Name: Region in which GuardDuty service is running. Make sure that the region name matches the region in the Profile ARN and Trust Anchor ARN.
- Detector ID: The Unique ID of the detector.
- Initial Range (in days): Number of days to pull the data for the initial run.


- Click Save.

Add a Business Rule for AWS GuardDuty
To share indicators fetched from the AWS GuardDuty to the Netskope CE you will need to have a business rule that will filter out the indicators that you want to share. To configure a business rule follow the below steps:
- Go to Threat Exchange > Business Rule and click Create New Rule.
- Add the filter according to your requirement in the rule.

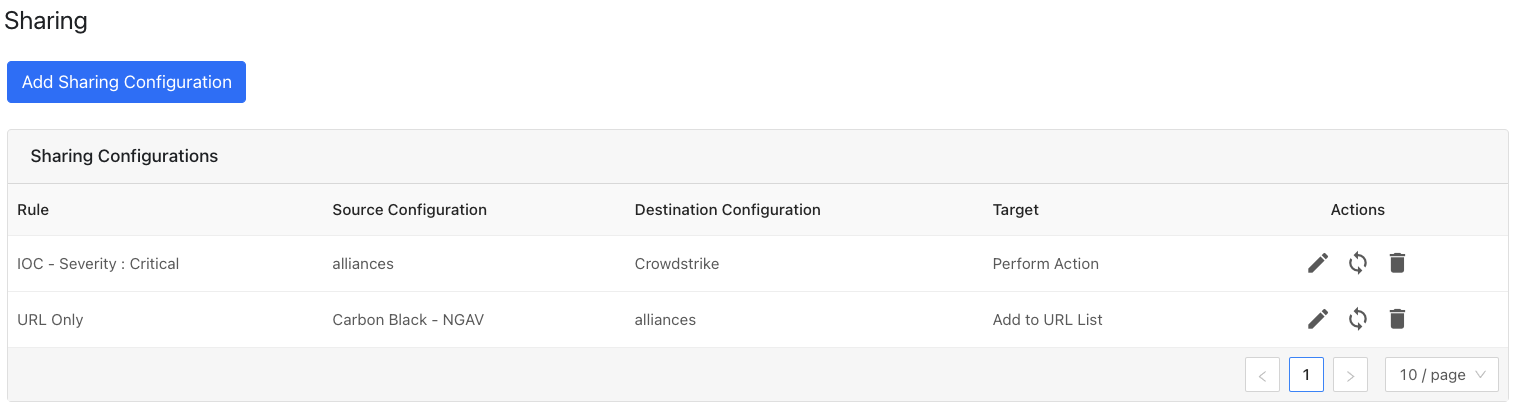
- Go to Threat Exchange and select Sharing. The Sharing page displays the existing relationships for each sharing configuration in grid view as shown below. The Sharing page also has inputs to configure new sharing from one plugin to another.
- Click Add Sharing Configuration, and in the Source Configuration dropdown list, select AWS GuardDuty.
- Select a Business Rule, and then select Netskope for the Destination Configuration. Sharing configurations are unidirectional. data obtained from one plugin is shared with another plugin.



- Select a Target. Each plugin will have a different target or destination for the IoC.
- For Add a File Hash List, enter a List Name, List Size, and Default File Hash. The List Name needs to exist in your Netskope UI at Settings > Policies > Profiles. For information about creating a File Profile for hashes, refer to Adding a File Profile
- Click Save.

Adding a new sharing configuration on the active source poll will share the existing IoCs of the source configuration to the destination configuration. Whenever a new sharing configuration is built, all the active IoCs will also be considered for sharing if they match the source/destination combination.
Note
Plugins that do not have API for ingesting data cannot receive threat data. This is true of the installed plugin API Source, which provides a bucket associated with an API endpoint for remote 3rd-party systems to push data to. Once a Sharing policy has been added, it takes effect.
After a sharing configuration has been created, the sharing table will show the rule being invoked, the source system providing the potential IoC matches, the destination system that will receive matching IoC, and the target applicable to that rule. Multiple Sharing configurations can be made to support mapping certain IoC to multiple targets even on the system destination system.
Modify, Test, or Delete a Sharing Configuration
Each configuration supports 3 actions:
- Edit the rule by clicking on the pencil icon.
- Test the rule by clicking on the synchronization icon. This tests how many IoC will actually be sent to the destination system based on the timeframe and the rule.
- Delete the rule by clicking on the garbage can icon.
Validate the AWS Guardduty Plugin
Validate the Pull
Pulled data will be listed on the Threat IoCs page. You can filter the IoCs pulled from the platform using the Filter: sources.source Like “<plugin name>”. You can filter the logs from CE as well with the plugin name.

On the AWS GuardDuty platform the Indicators are pulled from GuardDuty > Findings.

Validate the Push
To validate the push in Cloud Exchange, go to Threat Exchange > Logging and filter shared logs for Netskope.


To verify from the Netskope Tenant:
- Log in to your Netskope Tenant.
- Click Policies.
- Click File (for Sha256).
- Enter the File name that you used while configuring Sharing.

- For URLs: (IPv4 and Domain).
- Click Web > URL Lists.
- Click on the URL List which was used while configuring the sharing

Troubleshooting
If you face issue while configuring the plugin with Deployed on AWS
Check the IAM Role attached to your EC2 Machine.